Are you listed in Spamhaus? If so, here’s the Guide
This blog dives into the realm of public mirrors, explores the influential Spamhaus Project, sheds light on its error codes, and provides guidance for those finding themselves listed in Spamhaus.
In today’s digital landscape, ensuring the security and reliability of online content and email communication is paramount.
The Spamhaus Project is slowly introducing error codes for users of their Public Mirrors. When querying, it does not return IP or domain reputation data. Email administrators can encounter significant problems with their email streams if they don’t correctly configure the MTA to parse error codes. These configuration guides for common MTAs help those managing email infrastructure correctly set up their MTAs to avoid issues when parsing an error code.
Understanding the Spamhaus Project
The Spamhaus Project is an international organization that focuses on tracking and combating spam and other forms of online abuse. It operates a number of anti-spam and anti-malware systems, databases, and technologies to identify and block malicious activities.
Spamhaus maintains extensive databases of known spammers, spam sources, and other online threats, providing real-time protection and support to organizations and individuals.
By collaborating with internet service providers (ISPs), security companies, and law enforcement agencies, Spamhaus aims to create a safer and more secure online environment for users worldwide.
Understanding Public Mirrors
Public mirrors refer to copies or replicas of a particular website or service that are made available to the public. Separate servers host these mirrors to offer users alternative access points for retrieving the same content or data.
In the context of the Spamhaus Project, public mirrors are additional servers that host copies of the Spamhaus databases and services. Spamhaus sets up these mirrors in various global locations, enabling users to access data from nearby servers. Multiple mirrors distribute the load on the main server, improving availability and access speed.
The purpose of public mirrors is to provide widespread access to important resources, such as Spamhaus’s databases, making it easier for users to utilize the services and protect themselves from spam, malware, and other online threats.
Protecting Emails with Spamhaus’ MTA Public Mirrors.
“Spamhaus Project Public Mirrors using an MTA” refers to a system in which the Spamhaus Project makes its databases and services available to the public through multiple servers, using an MTA (Mail Transfer Agent) software.
In simple terms, Spamhaus maintains a network of servers that contain information about known spammers, malware, and other online threats. The public can access and use the Spamhaus databases on these servers to protect themselves from spam and malicious activities.
The servers use an MTA, which is a software responsible for sending and receiving emails, to handle the distribution of the Spamhaus databases. This ensures that the information is accessible to anyone who wants to utilize it to block or filter unwanted emails and protect their systems from potential threats.
By providing public mirrors using an MTA, the Spamhaus Project enables individuals, organizations, and internet service providers (ISPs) to leverage their databases and services effectively, enhancing the overall security and reliability of email communication.
This section contains instructions on how to leverage the features made accessible by your MTA to access the Spamhaus Project Public Mirrors.
1. Spamhaus Project Public Mirrors using Postfix
This guide explains how to use the Public Mirrors feature of Spamhaus Project with the Postfix Mail Transfer Agent (MTA) and configure SMTP-level rejections.
If you are using Postfix with Rspamd or SpamAssassin, it is not recommended to configure rejections at the SMTP level. Instead, use a milter and let SpamAssassin or Rspamd handle the filtering. This ensures they have the necessary information to effectively filter emails.
Configuring a milter and integrating it with SpamAssassin or Rspamd is beyond the scope of this guide. Seek assistance from your systems integrator if you need to do this.
SMTP-level blocking is suggested for moderate email volumes, limited computing resources, or when additional anti-spam software is not used.
To configure Postfix, make changes to the main.cf file.
Locate the smtpd_recipient_restrictions section and add the provided configuration lines, such as
smtpd_recipient_restrictions =
...
reject_rbl_client zen.spamhaus.org=127.0.0.[2..11]
reject_rhsbl_sender dbl.spamhaus.org=127.0.1.[2..99]
reject_rhsbl_helo dbl.spamhaus.org=127.0.1.[2..99]
reject_rhsbl_reverse_client dbl.spamhaus.org=127.0.1.[2..99]
warn_if_reject reject_rbl_client zen.spamhaus.org=127.255.255.[1..255]
Place these lines at the top of the section for optimal results.
After making the changes, reload the Postfix service using the appropriate command for your system.
Alternatively, you can use the postscreen daemon in Postfix for DNSBL lookup. Edit the main.cf file and add the line
postscreen_dnsbl_sites = zen.spamhaus.org=127.0.0.[2..11]
Then, reload the Postfix service.
By following these instructions, you can effectively utilize Spamhaus Project’s Public Mirrors feature and enhance your email security and filtering capabilities.
2. Spamhaus Project’s Public Mirrors Using Sendmail
This guide explains how to use Spamhaus Project’s Public Mirrors with the Sendmail MTA and provides instructions for configuring rejections at the SMTP level.
We recommend blocking emails at the SMTP level for those with a moderate email volume (over 200,000 emails per day), limited computing resources, or those who do not utilize additional anti-spam software.
To follow this guide, it assumes that your Sendmail configuration directory is located at /etc/mail. If it’s different on your system, make sure to adjust the path accordingly.
Whenever you encounter a box with a dollar sign ($), it means you should enter the command on your shell. Similarly, a box with a hash sign (#) indicates a command that needs to be executed with root privileges.
To begin the configuration process, edit your sendmail.mc file located in /etc/mail. Add the following line to the file, paying attention to the different types of quotation marks used.
FEATURE(enhdnsbl,`zen.spamhaus.org', `"554 Connecting client IP address listed in Spamhaus ZEN. See https://www.spamhaus.org/query/ip/"$client_address" for details"', `127.0.0.2', `127.0.0.3', `127.0.0.4', `127.0.0.9', `127.0.0.10', `127.0.0.11')dnl
After making the necessary changes, run the following commands with root privileges:
"m4 /etc/mail/sendmail.mc > /etc/mail/sendmail.cf" and
"/etc/init.d/sendmail reload".
This will generate the new sendmail.cf file and reload the Sendmail service.
Following these steps will enable you to utilize Spamhaus Project’s Public Mirrors in conjunction with Sendmail to enhance email security and mitigate spam threats.
3. Spamhaus Project Public Mirrors using Microsoft Exchange
Here’s how you can use Public Mirrors with Microsoft Exchange to reject emails at the SMTP level.
These steps are specifically for Exchange 2010 and newer versions.
To configure it, open Exchange Powershell as an administrator and enter the following commands:
add-IPBlockListProvider -Name 'Spamhaus ZEN' -LookupDomain 'zen.spamhaus.org' -Enabled $true -BitmaskMatch $null -IPAddressesMatch '127.0.0.2','127.0.0.3','127.0.0.4','127.0.0.9','127.0.0.10','127.0.0.11' -Priority '1' -AnyMatch $false -RejectionResponse 'Connecting IP address {0} has been blocked by Spamhaus ZEN. See http://www.spamhaus.org/query/bl?ip={0} for further details.'
Organizations can block known spam sources and protect their email infrastructure by checking incoming emails against the Spamhaus database. The integration helps in maintaining a secure and reliable email environment for businesses using Microsoft Exchange.
Spamhaus Project’s Error Codes: Decoding Email Filtering
Spamhaus Project’s error codes are a set of numerical identifiers that indicate specific conditions or issues related to email deliverability. Each error code represents a unique situation and provides information about the reason behind email rejection or blockage.
1. 127.0.0.6 – CBL. (Composite Blocking List): This code indicates that the IP address is listed on the Composite Blocking List, which focuses on identifying and blocking IP addresses involved in botnet activities and spam distribution.
2. 127.0.0.7 – DROP. (Don’t Route or Peer): This code indicates that the IP address is listed on the DROP list, which contains IP addresses that should not be routed or peered with due to their involvement in spam, malware, or other abusive activities.
3. 127.0.0.5 – CSS. (Composite Blocking List): This code indicates that the IP address is listed on the Composite Blocking List, which combines multiple reputable blocklists to identify and block spam sources..
4. 127.0.0.16 – DCC. (Distributed Checksum Clearinghouse): This code indicates that the email content has been flagged by the Distributed Checksum Clearinghouse, which identifies bulk email and spam based on checksums.
5. 127.0.0.10 – ZEN. (Combined Block List): This code indicates that the IP address is listed on the ZEN block list, which combines multiple Spamhaus blocklists to provide comprehensive spam detection.
6. 127.0.0.20 – DUHL. (Dial-Up/DSL Users Hijacked): This code indicates that the IP address is associated with dial-up or DSL users and has been hijacked for malicious purposes.
These error codes enable email administrators, service providers, and users to comprehend the specific reasons for flagging an email as spam. Some common error codes include DNSBL listings, policy violations, IP reputation issues, and spam-related activities.
How to proceed if you end up on the Spamhaus list
Take prompt action to resolve your listing in Spamhaus and restore your email reputation. Here are some essential steps to follow:
1. Begin by comprehending the reason for your listing. Spamhaus provides error codes and listings that indicate the reason for the listing, such as sending spam emails or having a compromised server.
Here are few examples of error codes:
| Error Code | Zone | Description |
| 127.0.0.2 | SBL | IP addresses involved in spamming or other malicious activities. |
| 127.0.0.14 | ROKSO | IP address or associated domain name is listed in the Register of Known Spam Operations |
| 127.0.0.3 | XBL | IP addresses associated with botnets or compromised systems used for malware distribution. |
| 127.0.0.9 | DBL | domain name associated with the email is listed on the Domain Block List |
| 127.0.0.4 | PBL | IP addresses that should not be delivering unauthenticated email directly to end users. |
| 127.0.0.18 | UBE | IP address is listed as a source of unsolicited bulk email |
2. Once you know the reason for the listing, investigate your email system or server for any security vulnerabilities or misconfigurations.
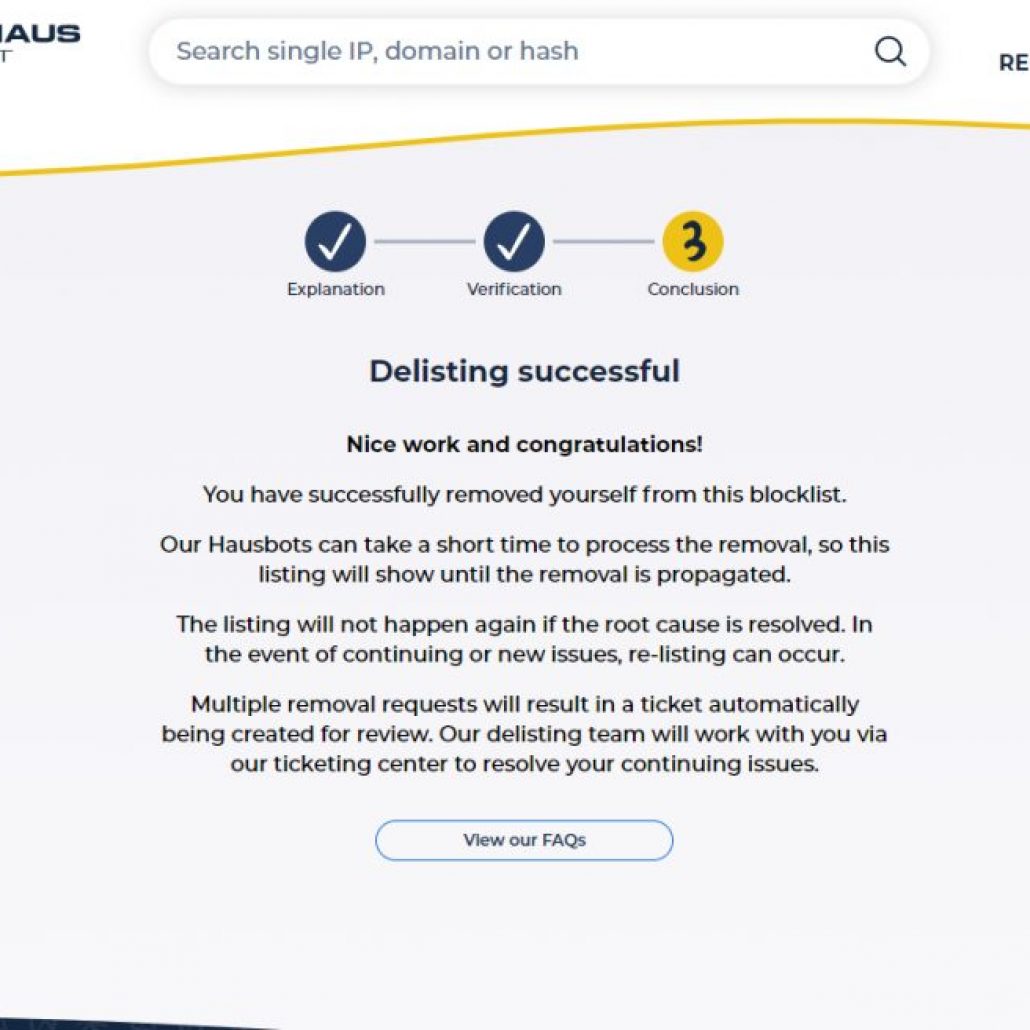
3. To remove your listing from Spamhaus, you need to follow their delisting process. This typically involves demonstrating that you have resolved the issue and taken steps to prevent future occurrences. Check Spamhaus’s website for specific instructions and follow them carefully.
4. After delisting, it’s crucial to monitor your email system regularly and maintain good email practices. Implement spam filters, update security measures, and educate your users about email best practices to prevent future listings.
5. If you’re unable to resolve the listing or need expert guidance, consider consulting with email deliverability professionals or IT specialists experienced in dealing with Spamhaus listings.
Remember, being listed in Spamhaus can impact your email deliverability and reputation.
Conclusion
Public mirrors and the Spamhaus Project are integral components in fortifying online security and maintaining a robust email ecosystem. Deciphering Spamhaus Project’s error codes, comprehending public mirrors, and removing listings enhance digital security.
Stay proactive, protect your online presence, and embrace the power of knowledge in the realm of public mirrors and the Spamhaus Project.

Leave a Reply
Want to join the discussion?Feel free to contribute!